Firefox is the window to the world for a lot of Linux users using Fedora, Ubuntu, or Mint. The "out-of-the-box" setup still leaves several doors open, despite the fact that it is likely the most private mainstream browser available. By default, it employs data-hungry search engines, gathers telemetry, and is vulnerable to "fingerprinting"—a method that tracks you even in the absence of cookies.You don't have to use a customised fork like LibreWolf in order to harden your browser. You can get the best of both worlds by modifying the official version: full control over your privacy and top-notch security upgrades.…

When you think about high-speed internet, it's easy to get fixated on the big players, the Comcasts and Coxes of the world.However, the "little guys"—regional co-ops, municipal ISPs, and small-town providers that maintain rural communities' connectivity—are undergoing a quiet revolution behind the scenes.Over the past year, Calix has demonstrated that providing a top-notch customer experience doesn't require a billion-dollar R&D budget. Calix is assisting smaller suppliers in automating their business models by embracing agentic AI, enabling them to compete on quality and service rather than just speed. AI as an "Operating Model" is the big play. Calix, back in 2026,…

High-stakes relationships in the tech industry frequently resemble fast-paced romantic relationships that ultimately result in a difficult and costly divorce. One of the most significant "marriages of convenience" in ten years is currently in its honeymoon stage: Apple and Google are collaborating to bring Gemini to the iPhone.Those who have followed these titans for decades notice a recurring pattern, and the conclusion typically involves Apple keeping the house while the partner is left wondering what happened to the furniture, even as the headlines center on the significant upgrade to Siri.Why Gemini is Apple's Only Option (For Now): Apple was late…

Researchers studying cybersecurity are alerting people to a subtle but perilous change in the digital environment. Malware that targets Industrial Control Systems (ICS), the digital "brains" that power our physical world, is no longer merely a theory in the lab; it is a quickly developing reality that has the capacity to immobilize contemporary society.According to a recent Comparitech analysis, hundreds of vital devices—from national railway networks to power grids—are left vulnerable on the public internet, just waiting to be discovered by the wrong person. Damage in the Real World: From Sub-Zero Temperatures to Screens ICS malware transcends the cyber-physical barrier,…
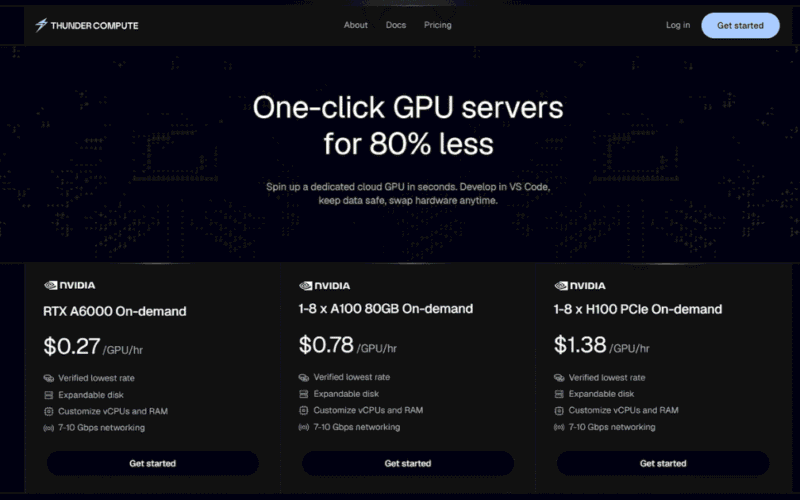
GPUs are the new currency in the current AI goldrush. But for many startups and independent researchers, high-performance compute – such as the much-sought-after NVIDIA A100s or H100s – often comes with eye-watering costs, inflexible multi-year contracts and endless discussions with sales reps. Thunder Compute is here to change that story. The startup just announced a $4.5 million seed round led by Matrix Partners, with heavy hitters like Y Combinator and Preston-Werner Ventures joining the mix. But this is not just another funding story; it’s a change in how we think about AI infrastructure. Why Thunder Compute is Different (It’s…

